What is 2FA (two-factor authentication)? - IBM
Two-factor authentication (2FA) verifies a user’s identity by asking for two pieces of proof, such as an online account password and a one-time passcode.
What is MFA (multifactor authentication)? - IBM
Multifactor authentication (MFA) verifies a user’s identity by requiring at least two forms of proof, such as a password, fingerprint or other biometric data.
Reset two-factor authentication for a user - IBM
If two-factor authentication (2FA) is enabled in IBM® NS1 Connect® and a user no longer has access to the 2FA device on which they set up 2FA, you can reset the 2FA key for the user.
Configuring authentication factors - IBM
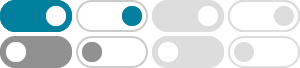
Verify supports two-factor authentication. It's a type of multifactor authentication that involves the use of a second factor, typically a system-generated code that the user must provide to prove their identity. …
Managing your IBM Verify authenticators
Configure and manage authentication factors for two-step verification (2FA) to secure your IBM Verify account. Two-step verification (2FA) enhances account security by requiring a second authentication …
什么是 2FA(双因素身份验证)?| IBM
双重身份验证 (2FA) 是一种验证用户身份的方法,它要求用户提供两项证明,例如在线帐户的密码(第一个因素)和身份验证应用程序的一次性密码(第二个因素)。
Managing two-factor authentication - IBM
Enforce two-factor authentication for all users You can add an extra layer of protection to your IBM NS1 Connect® organization's account by enforcing two-factor authentication (2FA). Enable two-factor …
RBI’s new authentication directions: Strengthening digital ... - IBM
Mar 6, 2026 · By reinforcing two-factor authentication and introducing a targeted dynamic-factor requirement for non-card-present transactions, the RBI continues its long-standing approach of …
Authentication vs. Authorization: What's the Difference? | IBM
Authentication verifies a user’s identity, while authorization gives the user the right level of access to system resources.
IBM Verify application
For a more comprehensive list of services that use two-factor authentication, see: https://twofactorauth.org Which mobile devices are supported by IBM Verify? IBM Verify supports …